Zero Trust Data Security: Protecting the Asset, Not the Perimeter
When a cloud provider suffers a misconfiguration exposing 100 million records, the question isn't "how did they get past the firewall?" there was no meaningful firewall. The question is: "why did those records exist in plain text? Why did that service account have access to all of them? And why did no one notice for months?" Zero Trust data security answers each of those questions with architecture. Gartner defines zero trust as "a security paradigm that explicitly identifies users and devices and grants them just the right amount of access so the business can operate with minimal friction while risks are reduced."
"Assume breach. Every system, every user, every service call is potentially compromised. Now design accordingly."
The State of Zero Trust Adoption (Gartner, 2024)
Gartner's 2024 survey of 303 security leaders found 63% of organizations have fully or partially implemented a zerotrust strategy. Yet in the same period, Gartner predicted only 10% of large enterprises will have a mature and measurable zerotrust program by 2026 up from less than 1% in 2022. Gartner also predicts that through 2026, more than half of cyberattacks will target areas that zerotrust controls don't cover or mitigate, reinforcing that zero trust is riskreduction, not riskelimination.
Gartner's January 2026 Prediction: ZeroTrust Data Governance
In January 2026, Gartner issued a landmark new prediction: by 2028, 50% of organizations will implement a zerotrust posture specifically for data governance, driven by the proliferation of unverified AIgenerated data. As LLMs increasingly train on outputs from prior models, the risk of "model collapse" where AI responses no longer reflect reality requires verifying data provenance before it enters any training pipeline. Gartner's "Predicts 2026: AIDriven, Automated, ZeroTrust Governance" formalizes this as a governance architecture requirement. According to the 2026 Gartner CIO Survey, 84% of respondents expect their enterprise to increase funding for GenAI in 2026, amplifying the urgency.
Machine Identities: Gartner's Underappreciated Risk
Gartner warns that machine identities API keys, service accounts, and automation credentials now dramatically outnumber human identities in most enterprises, and are frequently unmanaged. This is one of the largest unaddressed attack surfaces in enterprise data security. Every data pipeline, every ML training job, and every API integration generates machine identities requiring the same rigor as human access: rotation, leastprivilege provisioning, and behavioral anomaly monitoring.
ColumnLevel Security and Dynamic Masking
Modern cloud warehouses (Snowflake, BigQuery, Databricks) support columnlevel security policies and dynamic data masking returning a transformed version of a column based on the querying principal's role, without duplicating the data. A data analyst sees "************4242"; an engineer with elevated rights sees the full PAN. This approach is far more maintainable than maintaining separate sanitized copies of sensitive tables, and keeps accesscontrol logic centralized and auditable.
Confidential Computing
Gartner's 2025 cybersecurity predictions identify confidential computing alongside machine identity management and AInative security platforms as pivotal for building organizational resilience. Hardwareisolated execution environments (Intel TDX, AMD SEV, AWS Nitro Enclaves) enable encryptioninuse: even cloud providers cannot inspect data being processed. IBM's Cost of a Data Breach Report 2025 found organizations with extensive AI and automation in security save $2.2 million per breach compared to those without.
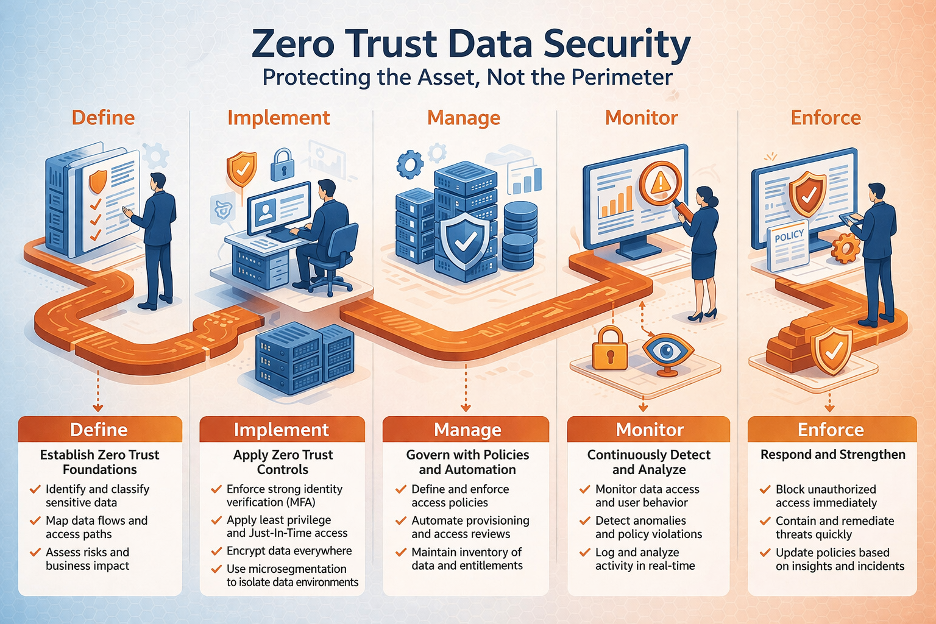
Building a Zero Trust Data Security Program
Classify all data assets by sensitivity using AIpowered classification engines at scale
Implement ABAC (attributebased access control), not static rolebased models with stale entitlements
Deploy dynamic data masking at the warehouse and API layer for all PII and sensitive fields
Centralize secrets management eliminate hardcoded credentials across all pipelines
Audit every data access event using MLbased behavioral analytics, not just failures
Extend zero trust to machine identities: service accounts, API keys, pipeline credentials
Include AI training data provenance review for all model training runs
Evaluate confidential computing environments for your highestsensitivity regulated workloads